Project Name
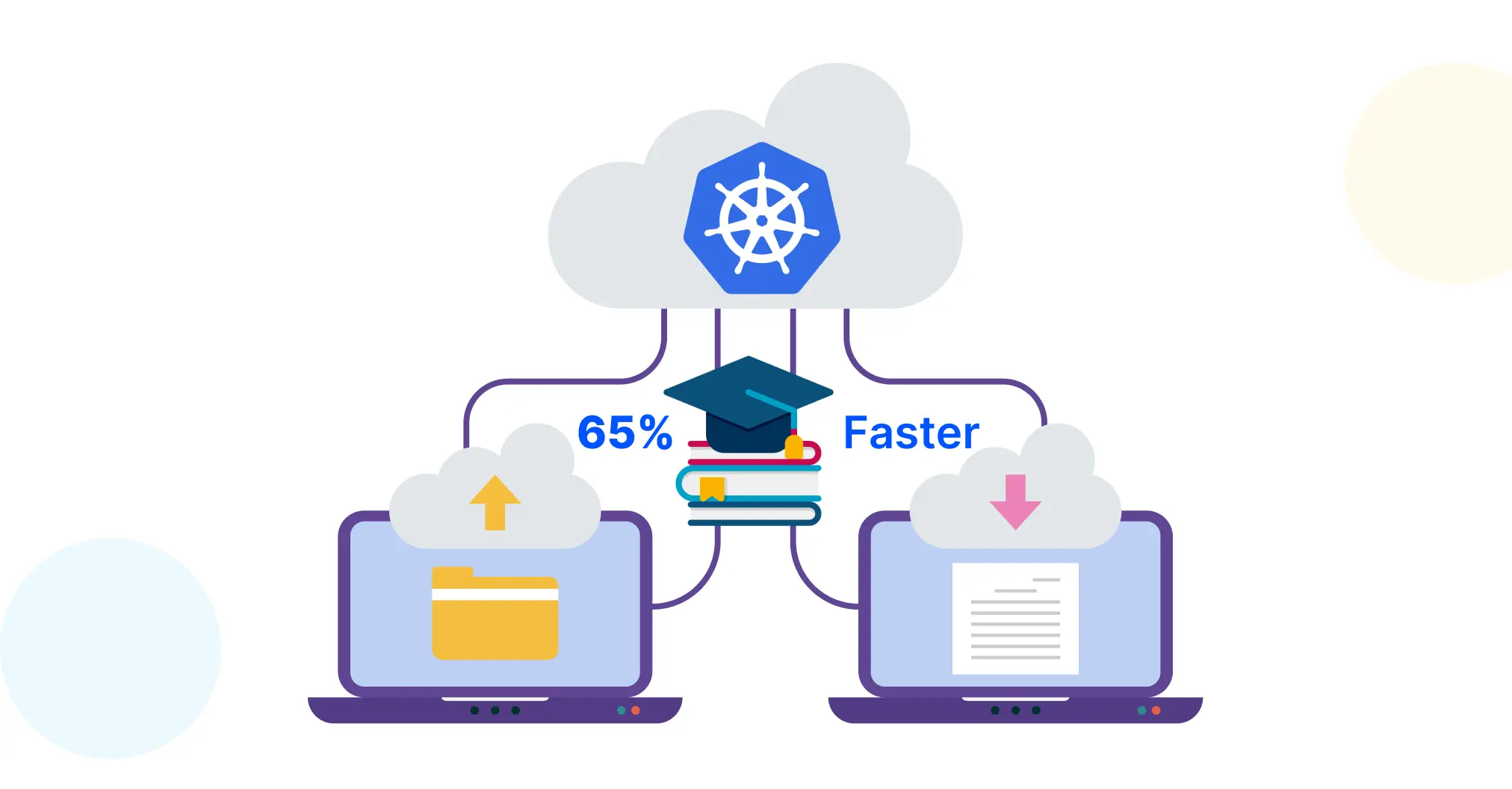
How an EdTech Platform Cut Deployment Time by 65% with an AI-Augmented Kubernetes Migration
![]()
A mid-size online learning and assessment platform operating across three regional markets had built its course delivery infrastructure on a setup that worked at launch and struggled at scale. By the time the engineering team flagged the problem formally, the platform was serving over 2 million daily active learners on VMs that required constant manual attention, had no autoscaling policy for exam-window and enrollment-surge traffic, and carried data privacy compliance exposure across every containerised workload.
The platform needed a production-grade Kubernetes migration, not a partial containerisation effort. Ksolves designed and executed a full AWS EKS migration covering all sixteen core services, including the course delivery API, assessment engine, and video streaming pipeline, without taking learning sessions offline once.
AI-augmented delivery compressed the engagement to up to 30% less than the standard timeline. Every phase, from architecture design and Helm chart packaging to compliance policy authoring and runbook documentation, was accelerated by AI tooling used daily across the Ksolves delivery team. The outcome: a 65% reduction in deployment time, a 99.95% uptime record in the first quarter post-migration, and a data privacy audit posture that no longer required a manual evidence sprint before every assessment cycle.
-
Manual Release Process Across Multi-Environment Infrastructure
Every production release required SSH access to servers in sequence, image pulls, service restarts, and manual health validation. A standard deployment took four to five hours and involved two engineers. Any mid-release failure left the environment in a partially updated state with no automated recovery path. Content update requirements added a review gate that extended release cycles further. The team was shipping eight to ten releases a month and treating each one as a planned risk event. -
Learner Traffic Spikes Without Autoscaling
The course delivery API and assessment engine carried the highest load. During exam windows, semester enrollment periods, and live-class events, traffic regularly spiked to 6x to 8x baseline. Fixed VM provisioning meant the infrastructure was either over-resourced and expensive during off-peak hours, or under-resourced and degraded during peak ones. Two platform degradation incidents in the prior year, each lasting over 90 minutes, were traced directly to the absence of autoscaling for high-concurrency learning workloads. -
Data Privacy Compliance Without Audit Infrastructure
Learner data moved through APIs and shared volumes without consistent encryption enforcement, RBAC scoping, or tamper-resistant audit logging. Every compliance audit cycle required two to three days of manual evidence collection across engineers. There was no centralised record of who accessed what, when, or from which pod. The compliance posture existed on paper; it was not enforced or observable at the infrastructure level. -
No Centralised Observability Across Microservices
The platform had grown from three services at launch to sixteen. Logs lived on individual server disks. When a service degraded, engineers SSH'd into machines and grepped through logs manually. Mean time to detect a production issue was over 25 minutes, and the first signal was typically a support escalation from the learner success team, not an alert. There were no latency dashboards, no error rate visibility, and no cross-service trace correlation. -
Absence of Rollback Capability for Course Delivery Workloads
A bad release meant manually reverting the image, rebuilding, and redeploying. Recovery time regularly exceeded 50 minutes. For a platform running live assessments and synchronous classes, 50 minutes of degraded service is not an operational inconvenience; it is a learner experience and institutional credibility event. No versioned rollback mechanism existed. Incident reports noted the same root cause across three separate outages. -
Configuration Drift Across Environments
Staging, QA, and production had diverged through manual deployments over 18 months. Resource limits set in staging were not applied in production. Security policies validated in QA did not consistently carry through to live workloads. The team had introduced a change-freeze window before every major release cycle, which compressed the release calendar and created backlog pressure that made the problem self-reinforcing.
-
AI-Augmented EKS Cluster Design and Migration Planning
Ksolves designed a multi-node AWS EKS cluster with isolated node groups for stateless content delivery services and stateful data workloads, provisioned via Terraform. Development, staging, and production environments were separated by namespace with resource quotas and network policies enforced at the cluster level. Ksolves' AI-first Kubernetes migration approach accelerated the architecture review, compliance gap analysis, and infrastructure-as-code generation, compressing what would typically be a multi-week design phase to under two weeks without reducing validation depth. -
Helm-Based Service Packaging and GitOps Deployment Pipeline
All sixteen services were containerised and packaged as Helm charts with environment-specific value files. ArgoCD was configured to monitor Git repositories and automatically apply changes on merge, making every deployment declarative, auditable, and reversible. The Kubernetes GitOps pipeline eliminated manual release steps entirely. Drift detection ran continuously, flagging any deviation between declared configuration and running cluster state. -
Horizontal Pod Autoscaling with EdTech Workload Tuning
HPAs were configured on the course delivery API, assessment engine, and video streaming pipeline using two weeks of baseline learner traffic data to calibrate thresholds. For batch operations such as certificate generation and gradebook processing, KEDA was implemented to scale on queue depth rather than resource consumption, providing more responsive behaviour during end-of-semester processing cycles. Autoscaling configurations were validated under load simulation before go-live, covering both the exam-window spike pattern and the enrollment-burst pattern separately. -
Data Privacy Compliant Kubernetes Architecture
RBAC was scoped to least privilege across all service accounts. Secrets were managed via HashiCorp Vault with automated pod injection. Audit logs were shipped to a tamper-resistant central store on a continuous basis. OPA Gatekeeper blocked non-compliant deployments at admission time, meaning learner data environment policies were enforced at the cluster level before any workload reached production. The result was a compliance-ready Kubernetes architecture where audit evidence was generated automatically, not assembled manually before each review cycle. -
Centralised Observability Stack with AI-Assisted Anomaly Detection
Prometheus, Grafana, and Loki were deployed to cover metrics, dashboards, and log aggregation across all sixteen services. Per-service dashboards covered session throughput, latency percentiles, error rates, pod restarts, and resource saturation. An AI monitoring layer was added on top to detect deviations from per-service baselines, flagging memory pressure before OOM events and abnormal session failure rates before they escalated. Alerts were routed to the on-call channel via Alertmanager with pre-populated incident context. Mean time to detect dropped from 25 minutes to under 4 minutes in the first week. -
Zero-Downtime Migration with Parallel Traffic Routing
Kubernetes services were stood up alongside existing VMs, with traffic shifted service by service using weighted routing at the load balancer layer. Each service retained a VM fallback for 72 hours of stable cluster operation before being decommissioned. Course delivery continuity was maintained throughout. All sixteen services were migrated without a single unplanned outage.
-
65% Reduction in Deployment Time
Deployment time dropped from four to five hours to under 20 minutes. Monthly releases went from eight manual deployments to 35+ automated ones. Engineering time previously allocated to release coordination fell from over 30% of team capacity to under 5%. The capacity freed up cleared a 19-item product backlog that had been deferred for two quarters. -
Zero Session Downtime During Peak Load
The first major exam window post-migration processed 7.2x baseline concurrent session volume without degradation. Autoscaling absorbed the load before it reached service thresholds. The platform recorded 99.95% uptime across a 90-day window covering four peak traffic cycles. Infrastructure-related learner session escalations dropped to zero in the same period. -
Compliance Audit Time Cut
The next compliance audit cycle after migration completed almost 30% faster than the prior effort. Evidence was available on demand from the centralised audit console. No manual evidence collection sprint was required. Audit readiness became a continuous state, not a periodic effort. -
Observability Surfaced a Six-Month Production Issue
Three weeks after the observability stack went live, the team identified a memory leak in the video streaming pipeline that had been causing intermittent pod restarts for over six months. It had been invisible under the old setup. Mean time to detect dropped from 25 minutes to under 4. Mean time to resolve went from over 50 minutes to 16. -
Infrastructure Cost Reduced by 55%
Switching from always-on over-provisioned VMs to autoscaling node groups cut the monthly AWS bill by 55%. Savings came from right-sized pods terminating during off-peak windows and sixteen loosely managed instances consolidating into one efficiently scheduled cluster. The engagement paid for itself within four months. -
30% Faster Delivery than the Standard Timeline
Ksolves completed the full Kubernetes migration, covering EKS design, Helm packaging, GitOps pipeline setup, compliance hardening, and observability; everything was completed in 30% less time than standard timeline. AI-augmented delivery accelerated every phase: architecture review, Terraform module generation, Helm chart authoring, compliance policy drafting, and runbook documentation. Quality checkpoints were maintained throughout; the timeline compressed because the work was done more efficiently, not because steps were skipped.
This engagement shows what a well-executed Kubernetes migration delivers when it is designed around the operational realities of a high-concurrency EdTech platform: deployment reliability, demand-responsive autoscaling, continuously enforced compliance, and observability that finds problems before learners do. The engineering team moved from managing infrastructure to building products. That shift is the actual return on a Kubernetes migration done properly.
If your EdTech platform is running course delivery workloads on manually managed infrastructure without autoscaling, tested rollback, or audit-ready compliance enforcement, the exposure is already present. Talk to Ksolves about what a production-grade Kubernetes setup looks like for your environment.
Let’s talk about what a production-grade Kubernetes setup looks like for your platform.