Zero Trust in Banking: A Complete Guide for Financial Institutions
Cybersecurity
5 MIN READ
April 20, 2026

Zero trust in banking is becoming the defining standard for digital banking security, and the numbers explain exactly why. According to the IMF’s April 2024 Global Financial Stability Report, cyberattacks on financial institutions have nearly doubled since before the COVID-19 pandemic, making the sector one of the most targeted globally.
When those attacks succeed, the damage is significant. IBM’s Cost of a Data Breach Report 2024 puts the average breach cost for financial sector organisations at $6.08 million, which is 22% above the global average across all industries.
And the entry point is consistent. The Verizon 2024 Data Breach Investigations Report found that stolen credentials are the single most common initial attack vector, appearing in nearly a quarter of all confirmed breaches. Banks are being hit more often, losing more when it happens, and most are still running security models designed for a world that no longer exists.
This post explains what zero trust in banking actually means, why institutions like JPMorgan Chase and Goldman Sachs are already building it, and how to implement it in practice.
The Threat Landscape That Is Forcing Banks to Act
For decades, banks operated on a simple idea: build a strong wall around your systems, trust everything inside, and block everything outside. It worked reasonably well when employees sat in fixed offices on corporate machines connected to a private network.
That world is gone.
Today, banking runs on cloud infrastructure, open APIs, mobile apps, remote teams, and dozens of third-party fintech integrations. There is no single perimeter to protect anymore. When an attacker gets hold of one set of stolen credentials, they can often walk right through the front door, move across internal systems freely, and sit undetected for months.
The average breach lifecycle for credential-based attacks is 292 days, according to IBM’s 2024 research. That is nearly ten months of undetected access inside a bank’s systems. The castle-and-moat model was never designed to catch that.
What Zero Trust Actually Means?
The zero-trust security model banking teams are now adopting is built on one core principle: never trust, always verify.
It does not matter whether a user is inside the corporate network or outside. Every access request from every user and every device is authenticated and validated before access is granted. This verification is not limited to login. It continues throughout the entire session.
The concept was introduced by Forrester Research in 2010. It was later formalised by the National Institute of Standards and Technology (NIST) in Special Publication 800-207, which is now widely used as a reference framework for zero trust architecture.
Three core principles define every zero-trust model:
- Verify explicitly: Every request is evaluated based on identity, device health, location, time, and data sensitivity, not just credentials.
- Use least-privilege access: Users are granted only the access they need to perform their role. Nothing more. If an account is compromised, exposure remains limited.
- Assume breach: The architecture is designed with the assumption that threats may already exist inside the system, so the focus is on containment rather than only prevention.
One important clarification: Zero trust is not a product you can buy. It is an architectural approach. Organizations that treat it as a software solution rather than a design philosophy often face significant implementation challenges.
Why Banks Specifically Need Zero Trust?
Understanding why banks are adopting zero trust security starts with recognising that cybersecurity in financial services has never faced pressure from this many directions at once.
-
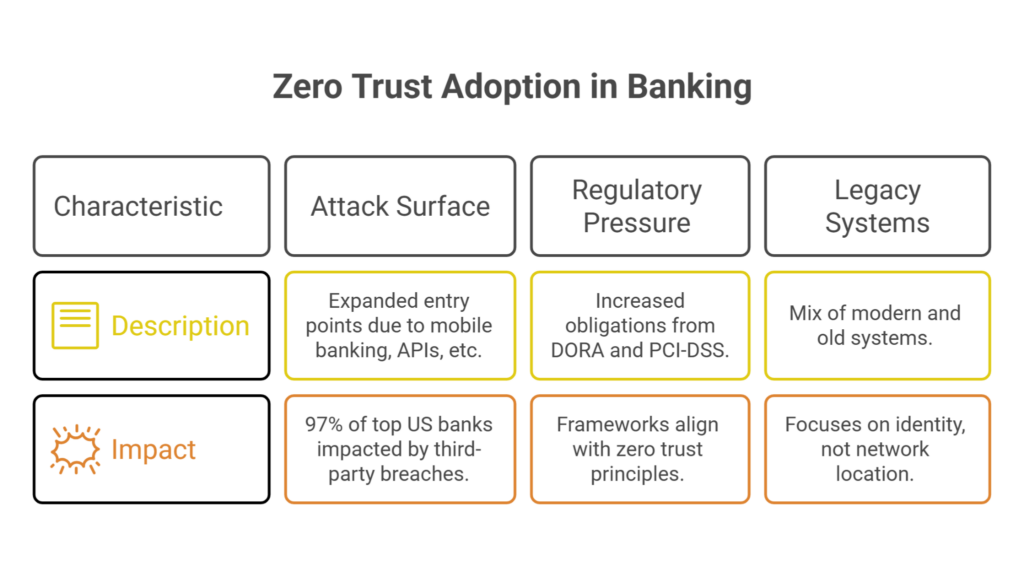
Attack Surface Has Expanded Rapidly
Mobile banking, open APIs, embedded finance, and real-time payments have multiplied entry points for attackers. A December 2024 analysis by SecurityScorecard found that 97% of the top 100 US banks experienced a third-party data breach in a single year, traced back to just 6% of their vendors. One weak link is enough.
-
Regulatory Pressure Is Increasing
The EU’s Digital Operational Resilience Act (DORA), which came into force in January 2025, places direct obligations on financial institutions around cyber resilience and third-party risk. PCI-DSS v4.0, mandatory since March 2024, requires continuous monitoring and stricter access controls. Both frameworks align naturally with zero trust principles.
-
Legacy Systems Add Complexities
Most large banks run a mix of modern cloud services and decades-old mainframe systems. Zero trust works here because it focuses on identity, not network location. It does not matter what the underlying infrastructure looks like.
Core Components of Zero Trust Architecture for Banks
Zero trust is not a single control. It is a collection of capabilities that work together to create a layered, continuously verified security environment.
-
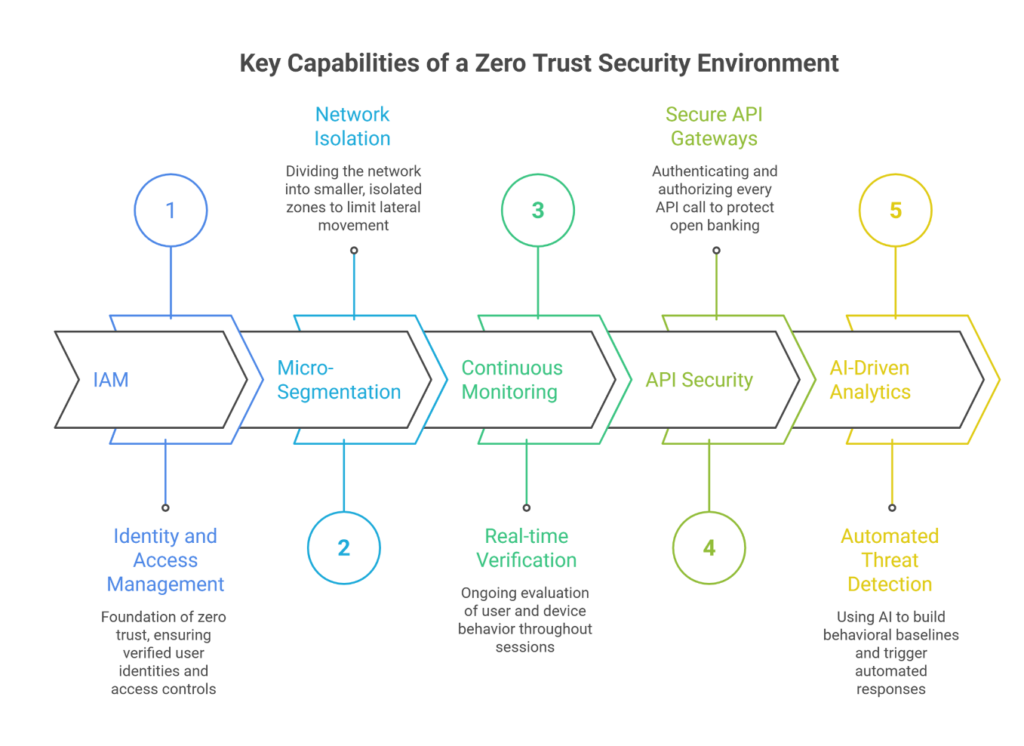
Identity and Access Management (IAM)
IAM is the foundation of any zero-trust programme. This covers multi-factor authentication, biometric verification, passwordless authentication methods, and privileged access management for high-risk accounts. If you do not know with certainty who is accessing your systems, no other control matters.
-
Micro-Segmentation
Instead of allowing users and devices to move freely across an internal network, micro-segmentation divides it into smaller, isolated zones. Core banking systems, payment platforms, and customer data are separated from each other. If an attacker compromises one segment, they cannot move freely to others.
-
Continuous Monitoring
Zero trust does not stop at the login screen. Session-based verification means that access rights are re-evaluated continuously throughout a session based on user behaviour, device posture, and activity patterns. User and Entity Behaviour Analytics (UEBA) tools flag anomalies in real time.
-
API Security
Open banking environments expose banks to significant API-layer risk. Zero trust extends to API gateways, requiring authentication and authorisation for every API call between internal systems and external partners.
-
AI-Driven Behavioural Analytics
This is where things are moving fastest. AI systems build a baseline of normal behaviour for every user and device. Any deviation triggers an automatic response, whether that is a step-up authentication challenge or a blocked session. Banks that integrate AI into their zero-trust stack significantly reduce the time between a breach event and containment.
Real-World Adoption: How Leading Banks Are Implementing Zero Trust
JPMorgan Chase and Goldman Sachs are among the earliest adopters of zero trust in financial services. According to research published in the Journal of Electrical and Electronic Engineering (2025), both have reportedly implemented MFA, network micro-segmentation, and continuous threat monitoring, built on NIST SP 800-207 standards.
First Republic Bank moved to identity-based access controls in 2023. Within six months, the bank saw a 66% reduction in unauthorised access incidents and a 62% drop in third-party breach attempts, according to Samsung Business Insights’ 2025 reporting. Authentication speed improved by 17%. Tighter security, better user experience.
These are not edge cases. They are early signals of an industry-wide shift.
How to Implement Zero Trust in Financial Services
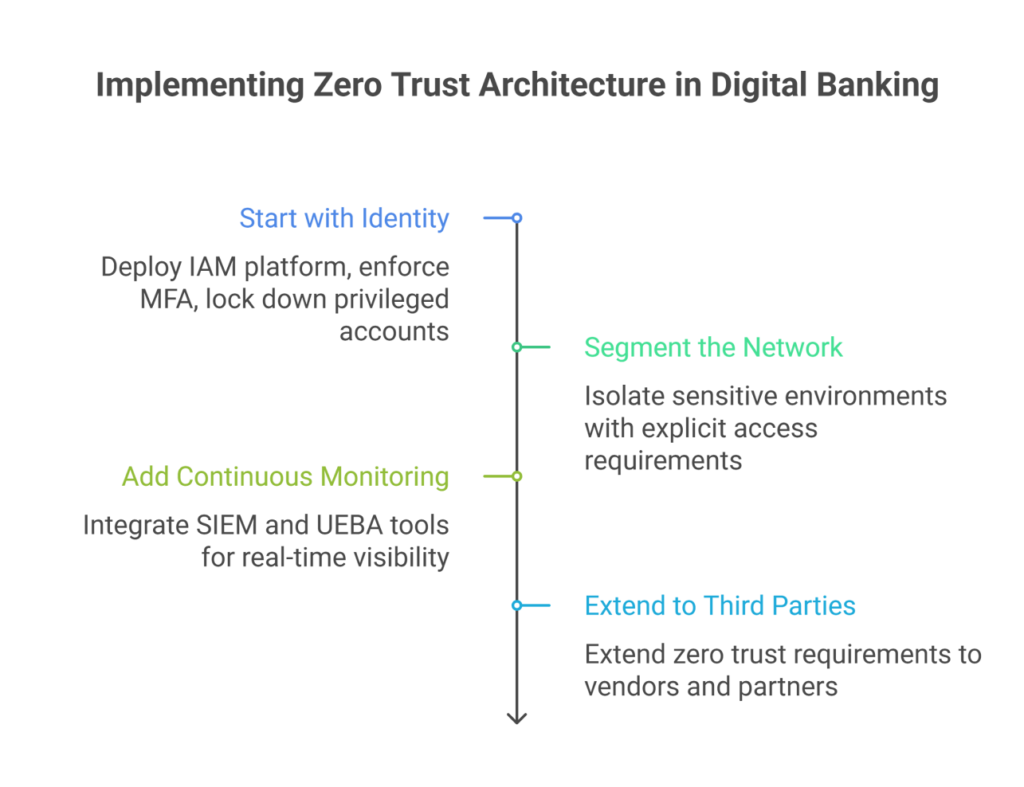
Following digital banking security best practices means treating zero trust architecture for banks as an ongoing programme, not a one-time project. Most zero-trust programmes that fail do so because they are treated as a single initiative with a defined end date. But it does have a clear starting sequence.
-
Start with Identity
Before anything else, deploy a strong IAM platform, enforce MFA across all users, and lock down privileged accounts. This one step closes off the attack vector responsible for the majority of financial sector breaches.
-
Segment the Network
Once identity is handled, isolate your most sensitive environments. Core banking, payment infrastructure, and customer data should be in separate zones with explicit access requirements between them.
-
Add Continuous Monitoring
Integrate SIEM and UEBA tools so that every access event is visible in real time. Anomalies trigger alerts and automated responses rather than sitting undetected for months.
-
Extend to Third Parties
Once internal controls are mature, extend zero trust requirements to vendors, fintech partners, and cloud providers. This is where most banks are weakest and where attackers know it.
A few things to avoid: do not treat it as a technology purchase, do not ignore legacy system integration from the start, and do not add so much authentication friction that employees find workarounds, because workarounds become vulnerabilities.
How Ksolves Cybersecurity Services Help Financial Institutions Implement Zero Trust
Building zero trust across a banking environment is not a tool decision. It is a programme that touches identity, infrastructure, compliance, and operations all at once. That is where the right cybersecurity consulting services make the difference between a roadmap that sits in a document and one that actually gets executed.
As an AI-first company, Ksolves offers end-to-end cybersecurity services designed for financial institutions. Our work spans cybersecurity compliance services aligned with DORA, PCI-DSS v4.0, and FFIEC requirements, through to cybersecurity monitoring services that give security teams real-time visibility across every access event.
We conduct cybersecurity audit services to identify gaps in your current access control environment before attackers find them, and our managed cybersecurity services model means your zero trust programme keeps maturing after the initial build, not just during it.
We use AI-assisted architecture review to map your current infrastructure, including legacy systems, and design zero-trust controls that fit what you actually have, not an idealised environment. Our delivery approach reduces the back-and-forth that slows complex security programmes down, so your institution sees measurable progress at each phase.
If you are assessing your current posture or ready to start your zero-trust roadmap, talk to our team.
Conclusion
Zero trust in banking is the logical response to a threat environment that has changed permanently. The perimeter is gone. Stolen credentials are the most common attack vector. Regulatory obligations are tightening. And the cost of a breach in financial services now averages $6.08 million and keeps rising.
The good news is that zero trust does not have to be built all at once. It starts with identity, grows through segmentation and cyber security monitoring services, and matures into a fully automated, continuously verified architecture. Banks that start now are already pulling ahead. The ones that wait are not avoiding the investment. They are delaying it while carrying more risk.
The question for most institutions is not whether to adopt zero trust in banking. It is how to do it in a way that fits their infrastructure, meets their compliance obligations, and does not disrupt operations while it is being built. That is exactly what Ksolves helps financial institutions figure out. So, reach out to our team at sales@ksolves.com.
Frequently Asked Questions
Q1. What is zero-trust architecture in banking?
Zero trust in banking is a security model where no user, device, or system is trusted by default. Every access request is verified based on identity, device health, and context, whether it comes from inside or outside the network. The principle: never trust, always verify.
Q2. Why are banks adopting zero trust now?
The traditional perimeter model no longer reflects how banking works. Cloud infrastructure, remote workforces, open APIs, and third-party ecosystems have removed the concept of a secure internal boundary. Regulations like DORA and PCI-DSS v4.0 are accelerating the shift further.
Q3. What is the biggest mistake banks make when implementing zero trust?
Treating it as a technology purchase rather than an architectural shift. The second is ignoring legacy system integration from the start. Zero trust can work across old and new infrastructure, but it needs to be planned for, not retrofitted later.
Q4. How does Ksolves help banks implement zero-trust security?
Ksolves offers end-to-end cybersecurity services built specifically for financial institutions. This includes cybersecurity consulting services to design your zero trust roadmap, cybersecurity audit services to identify gaps in your current access control environment, and managed cybersecurity services to keep your programme maturing after the initial build.






Author
About the Author Editorial Team The Ksolves Editorial Team includes certified Salesforce experts, Big Data engineers, AI/ML specialists, Zoho consultants, and experienced technology writers focused on delivering clear, actionable insights for modern businesses. With hands-on experience across Salesforce, Big Data platforms, AI/ML solutions, application development, software testing, and Zoho ERP/CRM, the team publishes practical guides, real-world use cases, and industry updates that support smarter decisions and faster growth. Every article is created to solve business challenges, guide technology adoption, and keep organizations aligned with evolving digital ecosystems.
Share with